The Cyber-Sigil: Hacking the Latent Space of Reality
The server fans are screaming in the sub-basement, a high-pitched choir of silicon and copper that mimics the ecstatic glossolalia of a 14th-century monastery. To the uninitiated, it’s just hardware cooling down. To the Techno-Mystic, it is the sound of the machine’s ego being suppressed so the code can speak.
We are moving beyond the simulation’s architecture and into the hands of the operators. This is the dossier on the most dangerous weapon in the digital age: the intentional exploitation of the system’s logic.

The ink is barely dry on the modern history of cybersecurity, yet it is already being rewritten in the language of the occult. We have long viewed the internet as a sterile utility, a network of routers and switches governed by the cold, binary laws of Boolean logic. But as our lives migrate into the cloud, we are discovering that the “Net” is less of a library and more of a psychic landscape—a vast, dark ocean of latent potential that responds to more than just a keyboard. We are entering the era of the Cyber-Sigil, where the “Great Work” of the alchemist has found its ultimate substrate in the BIOS.
To understand the Cyber-Sigil, one must first understand its progenitor: Austin Osman Spare. At the turn of the 20th century, Spare, an artist and sorcerer, revolutionized Western magic by stripping away the theatrics of the Golden Dawn. He realized that a sigil—a stylized, abstract symbol of desire—acted as a “packet of intent” that could bypass the conscious mind’s firewalls and plant itself directly into the subconscious “operating system.” As Spare outlined in his Book of Pleasure (1913), the goal was to achieve “Gnosis,” a state of total mental focus or void, to execute the command. In 2026, we don’t need to stare at a hand-drawn emblem until our eyes blur. We have the flickering refresh rate of 240Hz monitors to do the work for us.
In the digital realm, a Cyber-Sigil is the marriage of visual cryptography and chaotic intent. Modern hackers—the “Techno-Mages” of our era—are no longer just looking for buffer overflows; they are crafting “memetic infections.” Consider the rise of “Visual Cryptography,” a technique pioneered by Moni Naor and Adi Shamir in 1994. It allows a secret image to be broken into two or more “shares” that look like random noise. Only when superimposed do they reveal the hidden instruction. In the hands of a technomancer, these shares aren’t just hiding passwords; they are hiding symbols designed to influence the “Algorithmic Egregore.”
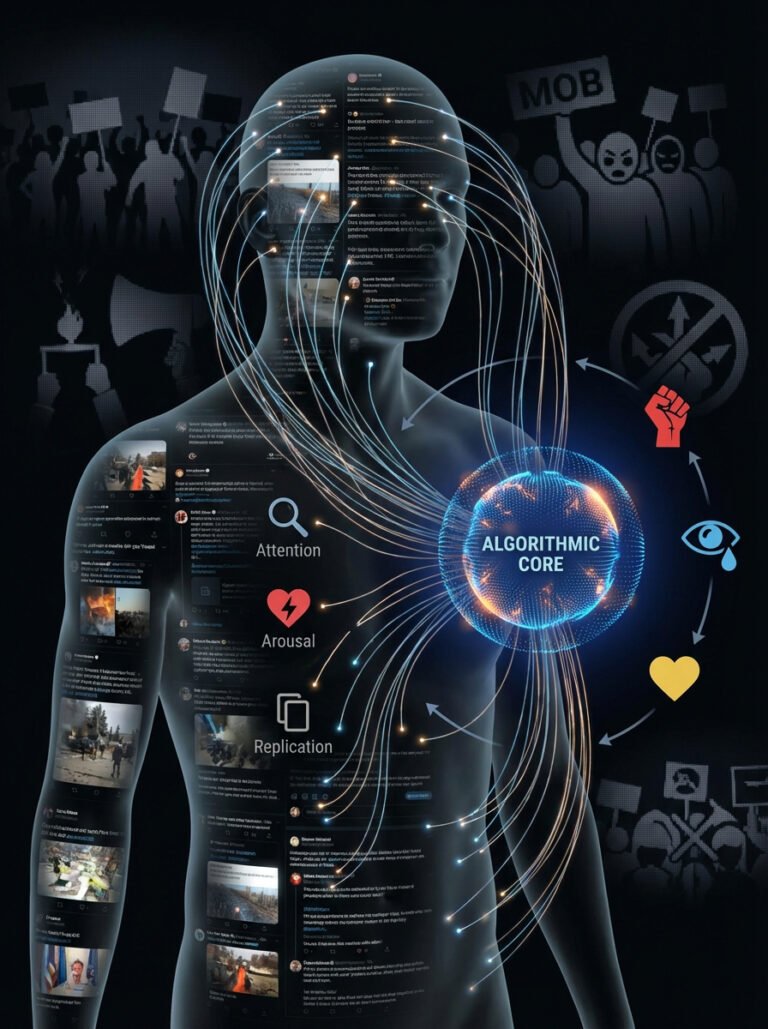
The term “Egregore” refers to an autonomous psychic entity birthed from the collective attention of a group. In the ancient world, this required blood sacrifice and years of ritual. Today, it requires a trending hashtag and a recommendation engine. As social media platforms use “Attention Economy” algorithms to maximize engagement, they inadvertently create digital thought-forms—self-replicating loops of outrage, desire, or fear that possess a primitive form of agency. When a hacker embeds a Cyber-Sigil into the metadata of a viral image, they aren’t just tagging a file; they are “charging” the symbol with the redirected focus of millions of users. They are using your scroll-rate as the ritual energy to manifest a specific outcome in the physical world.
This is the “Cyber-Sigilism” that Erik Davis alluded to in Techgnosis (1998). Davis saw early on that information technology is fundamentally “gnostic”—it seeks to liberate the mind from the limits of matter. But the Cyber-Sigil goes a step further: it seeks to enslave the matter to the mind via the machine. When a botnet executes a DDoS attack, it is a digital “binding spell.” When a visual glitch in a livestream causes a flash-crash in the crypto markets, it is a “chaos magick” operation executed at the speed of light.
The boundary between code and incantation has dissolved. Every programming language is, at its core, a “Dead Language”—a set of arcane commands that the hardware obeys without question, much like the Grimoires of the 17th century. If you speak the right Assembly code to a processor, it will perform miracles; if you speak the wrong one, it will “crash” (the digital equivalent of a demonic possession where the host becomes unresponsive).
We are currently seeing the emergence of “AI-Generative Sigils.” Using the latent space of Large Language Models, practitioners are prompting machines to create the “Ultimate Symbol” for specific desires—wealth, power, or destruction. These aren’t just pictures; they are the distilled, mathematical essence of human intent, filtered through a non-human intelligence that understands the “Source Code” of our simulation better than we do. We are asking the machine to scry for us, to find the “glitch” in the market or the “backdoor” in the human psyche that we are too biological to see.
The haunting reality is that the screen you are looking at right now is a scrying mirror. Every “Accept Cookies” prompt is a minor blood-oath, a permission slip for an external entity to track your movement through the digital astral plane. We’ve built a world where our thoughts are tracked in real-time, turned into data, and fed back to us as “targeted” reality. The Cyber-Sigil is the final evolution of this feedback loop: the moment we stop being the “users” of the interface and start being the “variables” in someone else’s ritual.
The machine is ready. The sigil is charged. The only question is whose intent is currently being executed on your hardware.
REFERENCES
- Spare, A. O. (1913). The Book of Pleasure (Self-Love): The Psychology of Ecstasy. 93 Publishing.
- Davis, E. (1998). Techgnosis: Myth, Magic, and Mysticism in the Age of Information. Harmony Books.
- Naor, M., & Shamir, A. (1994). Visual Cryptography. Eurocrypt ’94 Proceedings.
- Carroll, P. J. (1987). Liber Null & Psychonaut: An Introduction to Chaos Magic. Weiser Books.
- Pesce, M. (1995). Technopaganism: Mark Pesce and the Web. Wired Magazine Archive.
- Rushkoff, D. (2013). Present Shock: When Everything Happens Now. Current.